Dams can be targets for sabotage and terrorism.
Dams are often discussed in the context of natural hazards such as floods and earthquakes, but they are also part of the nation’s critical infrastructure and can be attractive targets for deliberate attack. Potential targets include dams, hydropower facilities, navigation locks, levees, and related water-control infrastructure that supports water supply, power generation, navigation, flood protection, and other essential services (US DHS, n.d.). Because a successful attack could cause downstream casualties and severe economic disruption, DHS has long treated dams as potential terrorist targets and emphasizes risk-informed protection and information-sharing between government and private owners/operators (US DHS, n.d.).
Protecting Dams Can Be Difficult
Protecting Dams Can Be Difficult
Compared with many other critical infrastructure assets, dams are large, geographically distributed, and frequently located in remote areas. Critical features can often be approached by land, water, and air creating real challenges for access control, surveillance detection, and law-enforcement response time (US DHS, 2012). At the same time, dams are generally robust structures designed to withstand extreme loads, so the most credible threats often involve exploiting site-specific vulnerabilities: limited redundancy in key mechanical/electrical components, constrained access routes that enable covert approach, or operational dependencies on control systems (US DHS, 2012).
Threat Pathways: Physical Attack, Insider Action, and Cyber Intrusion
A DHS historical threat resource summarizing real-world events between 2001 and 2011 documented 25 physical attacks on dams and related infrastructure worldwide and categorized common attack modes such as explosive devices (including IEDs), standoff weapons (rockets/mortars), assault teams, and incendiary devices (DHS 2012). These incidents affected not only dam embankments, but also power-generation equipment, control facilities, and appurtenant structures, components that may be easier to damage than the dam itself and can still create significant public safety and economic consequences (US DHS, 2012). In parallel, dam risk increasingly includes cyber-physical concerns. Modern dams often rely on industrial control systems (ICS) and supervisory control and data acquisition (SCADA) to monitor reservoir levels, operate gates and valves, and support remote or automated functions. Research on “human factors” in dam safety highlights that extraordinary human-caused incidents include sabotage, terrorism, and hacking of operating systems; expanding connectivity and remote control can increase exposure if cyber security practices are weak (Adamo et al. 2021). The following two case studies highlight how some of these threats have been carried out at actual dam structures.
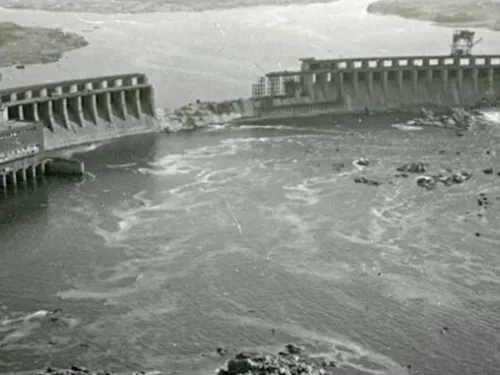
Case Study 1: Dnieper Hydroelectric Station (DniproHES), 1941 & 2022
One of the most consequential examples of deliberate dam damage occurred during World War II, when Soviet forces destroyed the Dnieper Hydroelectric Station (also known as DniproHES/Dneprostroi Dam) on August 18, 1941 to impede the advancing German army. Contemporary summaries note that approximately 20 tons of explosives were used and that roughly 100 meters (m) of the gravity arch dam were damaged (Miyamoto and Richards, 2021). The resulting flood wave reportedly moved downstream with little or no warning, inundating populated areas and affecting both civilians and military forces (Miyamoto and Richards 2021). Casualty estimates in secondary accounts vary widely (on the order of tens of thousands), but the incident is consistently cited as a stark example of how using dams as weapons can disproportionately impact civilians and create cascading humanitarian consequences (Adamo et al. 2021).
In 2022, the DniproHES was targeted again during Russia’s invasion of Ukraine. Ukraine’s State Hydropower Company reported that the facility was hit by Russian airstrikes with no risk of breach (The Guardian 2024). Other critical energy infrastructure were also targeted, showing the critical need to protect these assets during times of war (LLC Engineering Corp., 2025).

Case Study 2: Bowman Avenue Dam Cyber Intrusion, 2013
A modern illustration of cyber risk is the 2013 intrusion into the control system associated with Bowman Avenue Dam (New York). In a widely cited account summarized in dam safety literature, hackers gained access to the dam’s command-and-control system for a period and could have manipulated gate operations, except that a sluice gate had been manually disconnected for maintenance (Adamo et al., 2021). While the dam is small, the case is important because it demonstrated that even relatively minor facilities can be targeted and that successful intrusion to ICS/SCADA environments can create a pathway to physical consequences (Adamo et al., 2021; Miyamoto and Richards, 2021).
Key Lessons Learned for Dam Owners and Operators
- Treat Deliberate Attack as a Credible Loading Condition in Risk Management: DHS recommends that owners/operators identify sector assets and prioritize them based on consequence, vulnerability, and threat, recognizing that deliberate aggressor actions can contribute to a facility and portfolio risk (US DHS, n.d.; US DHS, 2012). For high-consequence facilities, integrating security considerations into existing dam safety risk frameworks helps ensure that protective investments are commensurate with consequences.
- Reduce Exposure Created by Publicly Available Sensitive Information: Security planning is complicated by the reality that dams are engineered systems with well-understood design principles, while at the same time many details (access routes, operational practices, drawings, and cybersecurity architecture) can materially increase risk if widely disclosed. DHS specifically notes that risk-related prioritization information should be protected from public release (DHS, n.d.).
- Build Layered Physical Security, Not Single-Point Defenses: Physical protection is most effective when it combines deterrence, detection, delay, and response. Pertinent DHS programs include Buffer Zone Protection Plans to improve security measures and local coordination around facilities and Site Assistance Visits to identify vulnerabilities spanning operations, crisis management, physical and cyber security, and interdependencies (DHS, n.d.). These approaches align well with the reality that dams often have large perimeters and multiple approach routes.
- Treat Cybersecurity as Dam Safety: Dam cyber incidents are fundamentally safety issues when they can alter releases, disable alarms, or degrade operator awareness. Increasing connectivity and remote operation can open pathways to cyber-attacks, and reports summarized in the literature point to common weaknesses such as boundary protection gaps and weak identification/authentication management (Adamo et al. 2021). Practical steps to improve cybersecurity include network segmentation of ICS/SCADA, multi-factor authentication for remote access, vendor and patch management procedures appropriate for control systems, logging/monitoring, and incident response playbooks that include manual backup operations.
- Prepare for “Attack on Appurtenances” Scenarios, Not Just Dam Breach: DHS’ incident summaries emphasize attacks on powerhouses, control buildings, and appurtenant structures (US DHS, 2012). For many dams, disruption or malicious operation of gates/valves, loss of station power, or damage to control systems may be more plausible than catastrophic structural failure but still capable of creating dangerous releases, jeopardizing critical power generation capabilities, or crippling response capability during extreme events.
- Strengthen Relationships and Hold Exercises with Emergency Management and Law Enforcement: Deliberate attacks unfold differently than floods or earthquakes: they may involve secondary devices, coordinated teams, misinformation, or concurrent cyber interference. It is a dam owner’s responsibility to identify site-specific security weaknesses, incorporate physical and cyber measures, remain vigilant, and maintain strong relationships with emergency management experts (Miyamoto and Richards, 2021). Regular joint drills that include security-driven scenarios help validate notification protocols, decision authority for rapid operational changes, and communication pathways.
- Avoid Complacency: Security Protocols Should Adapt to Threat Conditions: DHS notes that owners/operators of critical dams may increase security posture during heightened threat conditions and that effective sector security strategies benefit from understanding historical attack vectors and adversary capabilities (US DHS, 2012). Security should be revisited as staffing, technology, and threat landscapes evolve.
Moving Forward
The central lesson from both historical and modern examples is that deliberate attacks on dams can harm civilians, disrupt essential services, and create cascading consequences well beyond the dam site. The objective is not to turn dam owners into intelligence agencies, but to make dams harder targets: prioritize high-consequence assets, reduce exploitable vulnerabilities, implement layered physical and cyber protections, and integrate security scenarios into emergency planning and exercises (US DHS, n.d.; US DHS, 2012; Adamo et al., 2021).
References
(4) Miyamoto, C., & Richards, G. (2021). Dam Disaster in World War II: Destruction of the Dnieper Hydroelectric Station in 1941 [PowerPoint Presentation]. 2021 ASDSO Annual Conference. Association of State Dam Safety Officials.
(5) US DHS. (2012). Worldwide Attacks Against Dams: A Historical Threat Resource for Owners and Operators. National Protection and Programs Directorate, Office of Infrastructure Protection. United States Department of Homeland Security.
(6) US DHS. (n.d.). National Infrastructure Protection Plan: Dams Sector [Fact Sheet]. United States Department of Homeland Security.
This lesson learned was peer reviewed by Greg Richards, P.E. (GFT, Inc.).

Maple Grove Dam (Colorado, 1979)
Additional Case Studies (Not Yet Developed)
- DniproHES (Ukraine, 1941 & 2022)
- Bowman Avenue Dam (New York, 2013)
- Möhne and Edersee dams, British "Dambusters" raid / Operation Chastise (Germany, 1943)
- Hwachon Dam(Korea, 1951)
- Kajaki Dam (Afghanistan, 2005)
- Mytikyina (Myitsone) Dam (Burma/Myanmar, 2010)
- Hillsborough Dam (Florida, 1898)
National Infrastructure Protection Plan: Dams Sector
Dam Safety and Security in the United States
Dams Sector Cybersecurity Framework Implementation Guidance